Methods to confirm an information breach
[ad_1]
Through the years, Information World has extensively lined information breaches. In truth, a few of our most-read tales have come from reporting on large information breaches, comparable to revealing shoddy safety practices at startups holding delicate genetic data or disproving privateness claims by a preferred messaging app.
It’s not simply our delicate data that may spill on-line. Some information breaches can include data that may have vital public curiosity or that’s extremely helpful for researchers. Final 12 months, a disgruntled hacker leaked the interior chat logs of the prolific Conti ransomware gang, exposing the operation’s innards, and an enormous leak of a billion resident information siphoned from a Shanghai police database revealed a few of China’s sprawling surveillance practices.
However one of many greatest challenges reporting on information breaches is verifying that the info is genuine, and never somebody making an attempt to sew collectively faux information from disparate locations to promote to patrons who’re none the wiser.
Verifying an information breach helps each firms and victims take motion, particularly in instances the place neither are but conscious of an incident. The earlier victims learn about an information breach, the extra motion they’ll take to guard themselves.
Creator Micah Lee wrote a book about his work as a journalist authenticating and verifying massive datasets. Lee not too long ago printed an excerpt from his e book about how journalists, researchers and activists can verify hacked and leaked datasets, and find out how to analyze and interpret the findings.
Each information breach is completely different and requires a singular method to find out the validity of the info. Verifying an information breach as genuine would require utilizing completely different instruments and methods, and on the lookout for clues that may assist determine the place the info got here from.
Within the spirit of Lee’s work, we additionally needed to dig into a number of examples of information breaches we’ve got verified up to now, and the way we approached them.
How we caught StockX hiding its information breach affecting tens of millions
It was August 2019 and customers of the sneaker promoting market StockX obtained a mass e-mail saying they need to change their passwords as a consequence of unspecified “system updates.” However that wasn’t true. Days later, Information World reported that StockX had been hacked and somebody had stolen tens of millions of buyer information. StockX was compelled to confess the reality.
How we confirmed the hack was partially luck, but it surely additionally took numerous work.
Quickly after we printed a narrative noting it was odd that StockX would power probably tens of millions of its prospects to alter their passwords with out warning or rationalization, somebody contacted Information World claiming to have stolen a database containing information on 6.8 million StockX prospects.
The individual mentioned they had been promoting the alleged information on a cybercrime discussion board for $300, and agreed to supply Information World a pattern of the info so we may confirm their declare. (In actuality, we might nonetheless be confronted with this identical state of affairs had we seen the hacker’s on-line posting.)
The individual shared 1,000 stolen StockX person information as a comma-separated file, basically a spreadsheet of buyer information on each new line. That information appeared to include StockX prospects’ private data, like their title, e-mail deal with, and a replica of the client’s scrambled password, together with different data believed distinctive to StockX, such because the person’s shoe dimension, what system they had been utilizing, and what forex the client was buying and selling in.
On this case, we had an thought of the place the info initially got here from and labored below that assumption (except our subsequent checks recommended in any other case). In principle, the one individuals who know if this information is correct are the customers who trusted StockX with their information. The better the quantity of people that affirm their data was legitimate, the better probability that the info is genuine.
Since we can’t legally examine if a StockX account was legitimate by logging in utilizing an individual’s password with out their permission (even when the password wasn’t scrambled and unusable), Information World needed to contact customers to ask them straight.
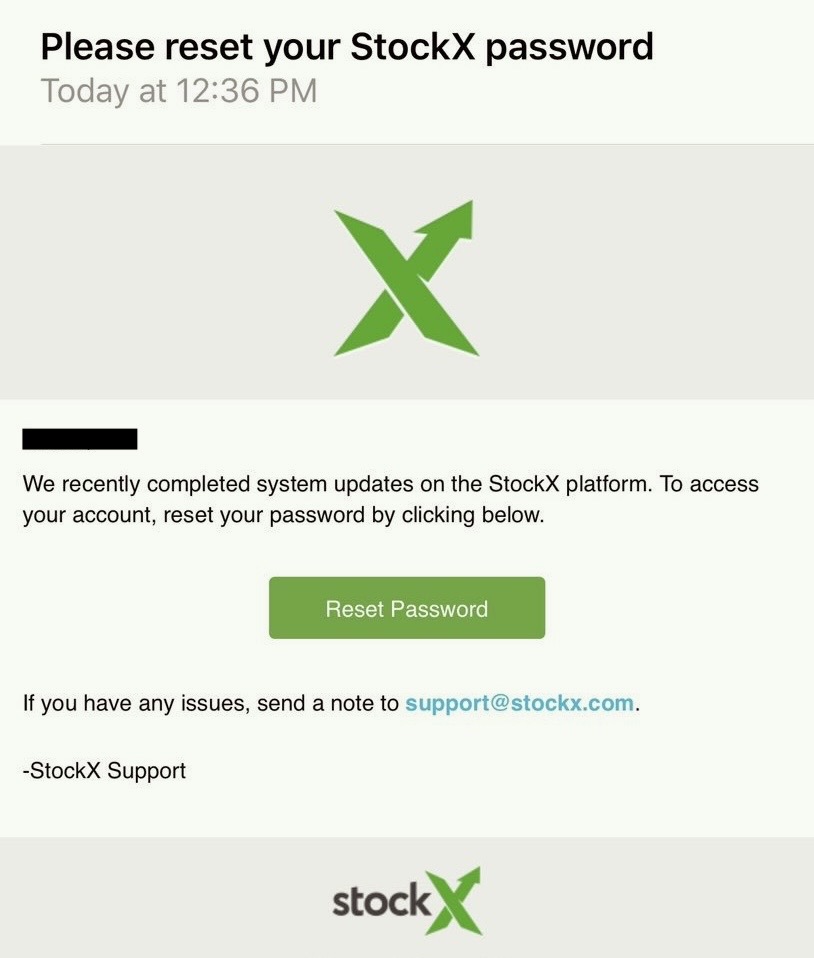
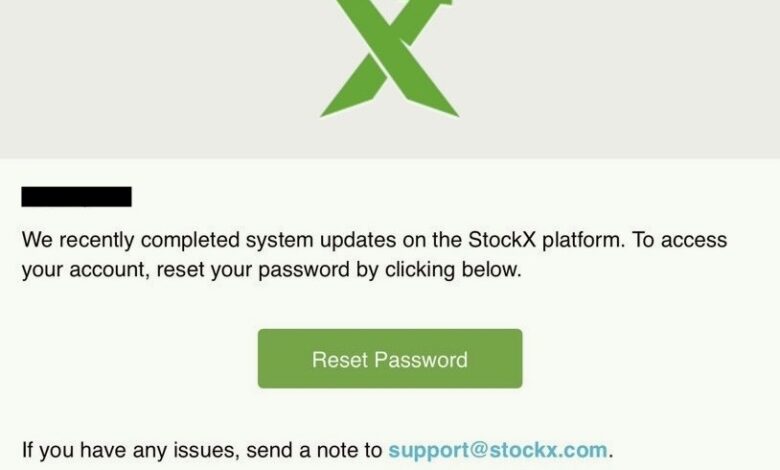
StockX’s password reset e-mail to prospects citing unspecified “system updates.” Picture Credit: file photograph.
We’ll usually search out individuals who we all know could be contacted shortly and reply immediately, comparable to by way of a messaging app. Though StockX’s information breach contained solely buyer e-mail addresses, this information was nonetheless helpful since some messaging apps, like Apple’s iMessage, enable e-mail addresses rather than a cellphone quantity. (If we had cellphone numbers, we may have tried contacting potential victims by sending a textual content message.) As such, we used an iMessage account arrange with a @techcrunch.com e-mail deal with so the folks we had been contacting knew the request was really coming from us.
Since that is the primary time the StockX prospects we contacted had been listening to about this breach, the communication needed to be clear, clear and explanatory and needed to require little effort for recipients to reply.
We despatched messages to dozens of individuals whose e-mail addresses used to register a StockX account had been @icloud.com or @me.com, that are generally related to Apple iMessage accounts. By utilizing iMessage, we may additionally see that the messages we despatched had been “delivered,” and in some instances relying on the individual’s settings it mentioned if the message was learn.
The messages we despatched to StockX victims included who we had been (“I’m a reporter at Information World”), and the rationale why we had been reaching out (“We discovered your data in an as-yet-unreported information breach and want your assist to confirm its authenticity so we are able to notify the corporate and different victims”). In the identical message, we offered data that solely they may know, comparable to their username and shoe dimension that was related to the identical e-mail deal with we’re messaging. (“Are you a StockX person with [username] and [shoe size]?”). We selected data that was simply confirmable however nothing too delicate that might additional expose the individual’s non-public information if learn by another person.
By writing messages this manner, we’re constructing credibility with an individual who could don’t know who we’re, or could in any other case ignore our message suspecting it’s some sort of rip-off.
We despatched comparable customized messages to dozens of individuals, and heard again from a portion of these we contacted and adopted up with. Normally a specific pattern dimension of round ten or a dozen confirmed accounts would recommend legitimate and genuine information. Each one who responded to us confirmed that their data was correct. Information World offered the findings to StockX, prompting the corporate to attempt to get forward of the story by disclosing the large information breach in an announcement on its web site.
How we found out leaked 23andMe person information was real
Identical to StockX, 23andMe’s latest safety incident prompted a mass password reset in October 2023. It took 23andMe one other two months to substantiate that hackers had scraped delicate profile information on 6.9 million 23andMe prospects straight from its servers — information on about half of all 23andMe’s prospects.
Information World found out pretty shortly that the scraped 23andMe information was probably real, and in doing so realized that hackers had printed parts of the 23andMe information two months earlier in August 2023. What later transpired was that the scraping started months earlier in April 2023, however 23andMe failed to note till parts of the scraped information started circulating on a preferred subreddit.
The primary indicators of a breach at 23andMe started when a hacker posted on a recognized cybercrime discussion board a pattern of 1 million account information of Ashkenazi Jews and 100,000 customers of Chinese language descent who use 23andMe. The hacker claimed to have 23andMe profile, ancestry information, and uncooked genetic information on the market.
But it surely wasn’t clear how the info was exfiltrated or even when the info was real. Even 23andMe mentioned on the time it was working to confirm whether or not the info was genuine, an effort that will take the corporate a number of extra weeks to substantiate.
The pattern of 1 million information was additionally formatted in a comma-separated spreadsheet of information, revealing reams of equally and neatly formatted information, every line containing an alleged 23andMe person profile and a few of their genetic information. There was no person contact data, solely names, gender, and delivery years. However this wasn’t sufficient data for Information World to contact them to confirm if their data was correct.
The exact formatting of the leaked 23andMe information recommended that every file had been methodically pulled from 23andMe’s servers, one after the other, however probably at excessive pace and appreciable quantity, and arranged right into a single file. Had the hacker damaged into 23andMe’s community and “dumped” a replica of 23andMe’s person database straight from its servers, the info would probably current itself in a distinct format and include extra details about the server that the info was saved on.
One factor instantly stood out from the info: Every person file contained a seemingly random 16-character string of letters and numbers, often called a hash. We discovered that the hash serves as a singular identifier for every 23andMe person account, but in addition serves as a part of the online deal with for the 23andMe person’s profile once they log in. We checked this for ourselves by creating a brand new 23andMe person account and on the lookout for our 16-character hash in our browser’s deal with bar.
We additionally discovered that loads of folks on social media had historic tweets and posts sharing hyperlinks to their 23andMe profile pages, every that includes the person’s distinctive hash identifier. Once we tried to entry the hyperlinks, we had been blocked by a 23andMe login wall, presumably as a result of 23andMe had fastened no matter flaw had been exploited to allegedly exfiltrate large quantities of account information and worn out all public sharing hyperlinks within the course of. At this level, we believed the person hashes could possibly be helpful if we had been capable of match every hash in opposition to different information on the web.
Once we plugged in a handful of 23andMe person account hashes into serps, the outcomes returned net pages containing reams of matching ancestry information printed years earlier on web sites run by family tree and ancestry hobbyists documenting their very own household histories.
In different phrases, a few of the leaked information had been printed partially on-line already. May this be outdated information sourced from earlier information breaches?
One after the other, the hashes we checked from the leaked information completely matched the info printed on the family tree pages. The important thing factor right here is that the 2 units of information had been formatted considerably otherwise, however contained sufficient of the identical distinctive person data — together with the person account hashes and matching genetic information — to recommend that the info we checked was genuine 23andMe person information.
It was clear at this level that 23andMe had skilled an enormous leak of buyer information, however we couldn’t confirm for positive how latest or new this leaked information was.
A family tree hobbyist whose web site we referenced for wanting up the leaked information advised Information World that they’d about 5,000 kinfolk found by way of 23andMe documented meticulously on his web site, therefore why a few of the leaked information matched the hobbyist’s information.
The leaks didn’t cease. One other dataset, purportedly on 4 million British customers of 23andMe, was posted on-line within the days that adopted, and we repeated our verification course of. The brand new set of printed information contained quite a few matches in opposition to the identical beforehand printed information. This, too, gave the impression to be genuine 23andMe person information.
And in order that’s what we reported. By December, 23andMe admitted that it had skilled an enormous information breach attributed to a mass scrape of information.
The corporate mentioned hackers used their entry to round 14,000 hijacked 23andMe accounts to scrape huge quantities of different 23andMe customers’ account and genetic information who opted in to a function designed to match kinfolk with comparable DNA.
Whereas 23andMe tried in charge the breach on the victims whose accounts had been hijacked, the corporate has not defined how that entry permitted the mass downloading of information from the tens of millions of accounts that weren’t hacked. 23andMe is now dealing with dozens of class-action lawsuits associated to its safety practices previous to the breach.
How we confirmed that U.S. navy emails had been spilling on-line from a authorities cloud
Typically the supply of an information breach — even an unintentional launch of non-public data — isn’t a shareable file full of person information. Typically the supply of a breach is within the cloud.
The cloud is a flowery time period for “another person’s pc,” which could be accessed on-line from anyplace on the planet. Which means firms, organizations and governments will retailer their recordsdata, emails, and different office paperwork in huge servers of on-line storage usually run by a handful of the Large Tech giants, like Amazon, Google, Microsoft, and Oracle. And, for his or her extremely delicate prospects like governments and militaries, the cloud firms provide separate, segmented and extremely fortified clouds for further safety in opposition to probably the most devoted and resourced spies and hackers.
In actuality, an information breach within the cloud could be so simple as leaving a cloud server related to the web and not using a password, permitting anybody on the web to entry no matter contents are saved inside.
It occurs, and greater than you may assume. Individuals truly discover them! And a few people are actually good at it.
Anurag Sen is a good-faith safety researcher who’s well-known for locating delicate information mistakenly printed to the web. He’s discovered quite a few spills of information over time by scouring the online for leaky clouds with the objective of getting them fastened. It’s a very good factor, and we thank him for it.
Over the Presidents Day federal vacation weekend in February 2023, Sen contacted Information World, alarmed. He discovered what seemed just like the delicate contents of U.S. navy emails spilling on-line from Microsoft’s devoted cloud for the U.S. navy, which must be extremely secured and locked down. Information spilling from a authorities cloud isn’t one thing you see fairly often, like a rush of water blasting from a gap in a dam.
However in actuality, somebody, someplace (and someway) eliminated a password from a server on this supposedly extremely fortified cloud, successfully punching an enormous gap on this cloud server’s defenses and permitting anybody on the open web to digitally dive in and peruse the info inside. It was human error, not a malicious hack.
If Sen was proper and these emails proved to be real U.S. navy emails, we needed to transfer shortly to make sure the leak was plugged as quickly as potential, fearing that somebody nefarious would quickly discover the info.
Sen shared the server’s IP deal with, a string of numbers assigned to its digital location on the web. Utilizing a web based service like Shodan, which routinely catalogs databases and servers discovered uncovered to the web, it was straightforward to shortly determine a number of issues in regards to the uncovered server.
First, Shodan’s itemizing for the IP deal with confirmed that the server was hosted on Microsoft’s Azure cloud particularly for U.S. navy prospects (often known as “usdodeast“). Second, Shodan revealed particularly what software on the server was leaking: an Elasticsearch engine, usually used for ingesting, organizing, analyzing and visualizing large quantities of information.
Though the U.S. navy inboxes themselves had been safe, it appeared that the Elasticsearch database tasked with analyzing these inboxes was insecure and inadvertently leaking information from the cloud. The Shodan itemizing confirmed the Elasticsearch database contained about 2.6 terabytes of information, the equal of dozens of onerous drives full of emails. Including to the sense of urgency in getting the database secured, the info contained in the Elasticsearch database could possibly be accessed by way of the online browser just by typing within the server’s IP deal with. All to say, these navy emails had been extremely straightforward to seek out and entry by anybody on the web.
By this level, we ascertained that this was virtually definitely actual U.S. navy e-mail information spilling from a authorities cloud. However the U.S. navy is big and disclosing this was going to be difficult, particularly throughout a federal vacation weekend. Given the potential sensitivity of the info, we had to determine shortly who to contact and make this their precedence — and never drop emails with probably delicate data right into a faceless catch-all inbox with no assure of getting a response.
Sen additionally supplied screenshots (a reminder to doc your findings!) displaying uncovered emails despatched from quite a lot of U.S. navy e-mail domains.
Since Elasticsearch information is accessible by way of the online browser, the info inside could be queried and visualized in quite a lot of methods. This may help to contextualize the info you’re coping with and supply hints as to its potential possession.
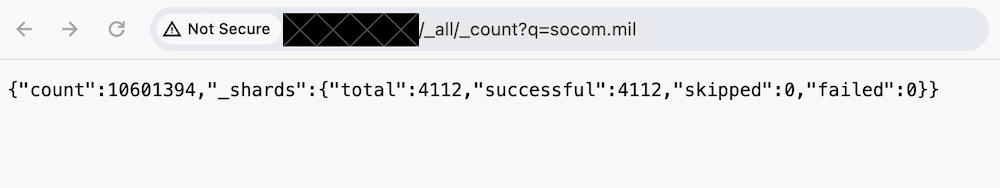
A screenshot displaying how we queried the database to rely what number of emails contained a search time period, comparable to an e-mail area. On this case, it was “socom.mil,” the e-mail area for U.S. Particular Operations Command. Picture Credit: Information World
For instance, most of the screenshots Sen shared contained emails associated to @socom.mil, or U.S. Particular Operations Command, which carries out particular navy operations abroad.
We needed to see what number of emails had been within the database with out taking a look at their probably delicate contents, and used the screenshots as a reference level.
By submitting queries to the database inside our net browser, we used the in-built Elasticsearch “rely” parameter to retrieve the variety of occasions a selected key phrase — on this case an e-mail area — was matched in opposition to the database. Utilizing this counting approach, we decided that the e-mail area “socom.mil” was referenced in additional than 10 million database entries. By that logic, since SOCOM was considerably affected by this leak, it ought to bear some duty in remediating the uncovered database.
And that’s who we contacted. The uncovered database was secured the next day, and our story printed quickly after.
It took a 12 months for the U.S. navy to reveal the breach, notifying some 20,000 navy personnel and different affected people of the info spill. It stays unclear precisely how the database grew to become public within the first place. The Division of Protection mentioned the seller — Microsoft, on this case — “resolved the problems that resulted within the publicity,” suggesting the spill was Microsoft’s duty to bear. For its half, Microsoft has nonetheless not acknowledged the incident.
To contact this reporter, or to share breached or leaked information, you will get in contact on Sign and WhatsApp at +1 646-755-8849, or by e-mail. You can even ship recordsdata and paperwork by way of SecureDrop.
[ad_2]
Source link